Finally, I managed to enable HTTPS on my own blog!
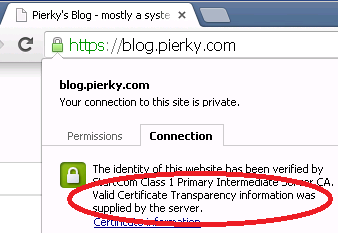
I opted for a quick-and-dirty solution based on a self-compiled version of HAProxy in front of WordPress, statically linked to OpenSSL 1.0.2, in order to serve Certificate Transparency information during the TLS setup.
Since 1.6 version, HAProxy supports Certificate Transparency (RFC6962) TLS extension and serves SCTs (Signed Certificate Timestamps) as part of the TLS handshake.
I used Janusz Dziemidowicz’s ct-submit.py script to submit my certificate to CT Logs and to dump raw TLS extension data of the received SCTs:
# curl -O https://gist.githubusercontent.com/rraptorr/2efaaf21caaf6574e8ff/raw/5e7e91f6e16a044a50cede67bfd8a059841151b2/ct-submit.py # python ct-submit.py ssl/MYCERT.pem -o ssl/MYCERT.pem.sctl
Then I downloaded and compiled OpenSSL as a static library:
# ./config --prefix=/tmp/openssl_static no-shared # make # make install
The same for HAProxy, statically linked to it:
# make TARGET=linux2628 USE_STATIC_PCRE=1 USE_OPENSSL=1 USE_ZLIB=1 SSL_INC=/tmp/openssl_static/include SSL_LIB=/tmp/openssl_static/lib ADDLIB=-ldl # make install
Then I simply configured HAProxy to be the front-end for my WordPress blog.
My small sct-verify script (more info on a previous post) can be used to verify it:
# ./sct-verify.py blog.pierky.com | egrep "Log found|Result|==" =========================================================== Log found : Aviator Result : Verified OK =========================================================== Log found : Pilot Result : Verified OK =========================================================== Log found : Rocketeer Result : Verified OK =========================================================== Log found : Certly Result : Verified OK
Next, sooner or later: HSTS, HPKP, DANE TLSA
Latest posts by Pier Carlo Chiodi (see all)
- Good MANRS for IXPs route servers made easier - 11 December 2020
- Route server feature-rich and automatic configuration - 13 February 2017
- Large BGP Communities playground - 15 September 2016